Network Defense:
Snort & Fail2ban.
Comparing Intrusion Detection vs. Prevention and implementing a layered defense strategy using custom Snort rules and Fail2ban jails.
In the previous case study, we observed how an attacker exploited an undefended system. This section focuses on Hardening. Intrusion Detection Systems (IDS) like Snort provide visibility, while Intrusion Prevention Systems (IPS) like Fail2ban actively block malicious actors.
1. Snort: The Network IDS
Snort is the de-facto standard for open-source IDS. It operates by packet sniffing and logging traffic that matches predefined signatures.
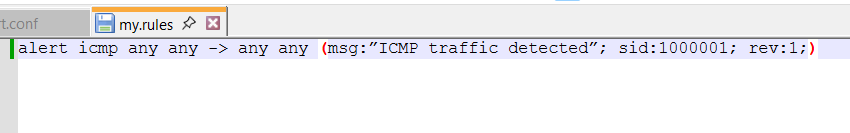
// CUSTOM_RULE: ICMP_Tunneling_Detection
A rule designed to detect large ICMP packets, often indicative of data exfiltration or tunneling attempts.
// CUSTOM_RULE: SSH_Brute_Force
While Snort can detect the volume of traffic, it works best when paired with a log analyzer. This rule flags excessive connection attempts.
2. Fail2ban: The Host IPS
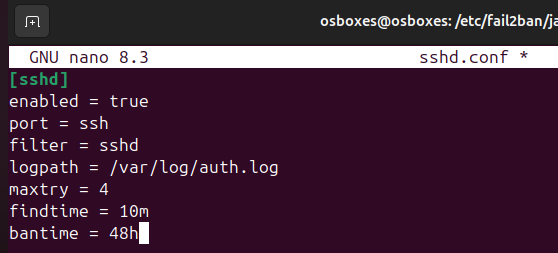
Fail2ban scans log files (e.g., `/var/log/auth.log`) and bans IPs that show malicious signs like too many password failures. It updates firewall rules (iptables) to reject new connections from those IP addresses.
// JAIL_CONFIGURATION: sshd
// JAIL_CONFIGURATION: vsftpd
3. Conclusion
By combining Snort's deep packet inspection with Fail2ban's active response capabilities, we create a robust defense-in-depth architecture. Snort provides the visibility needed to understand "what" is happening, while Fail2ban ensures that "action" is taken to stop it.