Investigation:
The "Mr. Evil" Compromise.
Using Autopsy to reconstruct a cyber attack, recover deleted artifacts, and map the attacker's footprint on a Windows XP legacy system.
Having established the legal frameworks (ACPO, NIST) in the previous chapter, this investigation applies those principles to a real-world scenario. The primary objective was to confirm illicit activity on a seized laptop while maintaining a strict chain of custody.
1. Evidence Acquisition
The evidence media was ingested into Autopsy 4.21.0. A hash verification (MD5) was performed to ensure the integrity of the image file matched the original seizure.
- Image Type: E01 (Expert Witness Format)
- Time Zone: CST (Central Standard Time)
- Operating System: Windows XP (with traces of a previous Windows 98 install)
2. Forensic Findings
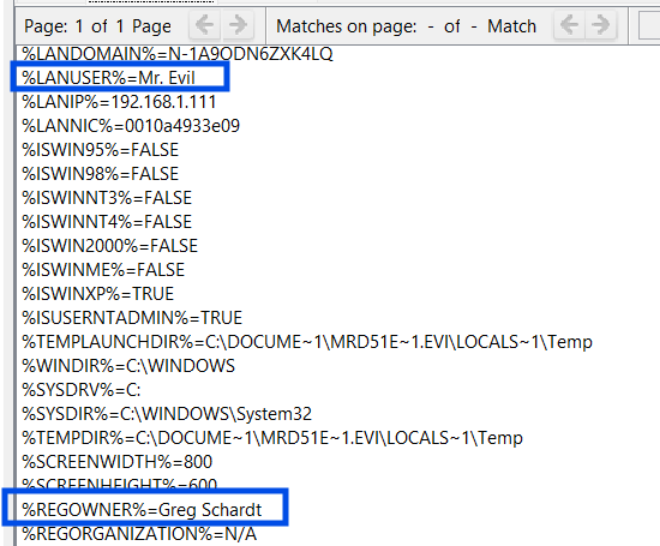
Registry analysis (`SAM` hive) identified the primary user account as "Mr. Evil". Additional cross-referencing with an `Irunin.ini` file linked this alias to a real name: "Gref Schardt".
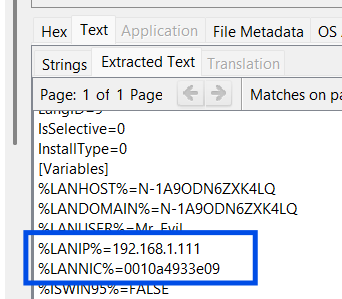
Device analysis revealed a Xircom CardBus Ethernet adapter. MAC address analysis confirmed the vendor OUI, linking physical hardware to network logs.
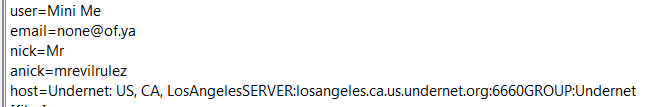
Artifacts from the mIRC client were recovered. Logs showed the user participating in an "ORC" channel, discussing hacking techniques and script usage.
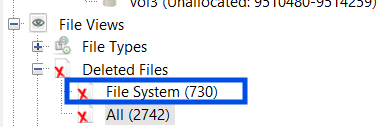
Autopsy's File System analysis recovered 730 deleted files. Critical executables were found hidden in the Recycle Bin (`DC1.txt`, `DC2.exe`), attempting to evade simple directory listings.
3. Technical Analysis
A deep dive into the Packet Capture (PCAP) files found on the desktop (`ethereal` captures) showed the user intercepting traffic from a Windows CE device accessing `mobile.msn.com`. This indicates active network sniffing and Man-in-the-Middle (MitM) attempts.
Furthermore, the presence of these tools typically triggers antivirus alerts, but the suspect had disabled system defenses, a common behavior in offensive security operations.
4. Conclusion
The investigation successfully attributed the system to the suspect "Gref Schardt" (Mr. Evil) and established a pattern of behavior consistent with black-hat hacking: tool acquisition, community discussion (IRC), concealment (Recycle Bin), and active execution (Network Sniffing). The chain of custody was maintained throughout, making these findings admissible.